Eclipse Attack Detection on a Blockchain Network

This paper introduces a novel non-parametric change detection algorithm to identify eclipse attacks on a blockchain network; the non-parametric algorithm relies only on the empirical mean and variance of the dataset, making it highly adaptable. An eclipse attack occurs when malicious actors isolate blockchain users, disrupting their ability to reach consensus with the broader network, thereby distorting their local copy of the ledger. To detect an eclipse attack, we monitor changes in the Fréchet mean and variance of the evolving blockchain communication network connecting blockchain users. First, we leverage the Johnson-Lindenstrauss lemma to project large-dimensional networks into a lower-dimensional space, preserving essential statistical properties. Subsequently, we employ a non-parametric change detection procedure, leading to a test statistic that converges weakly to a Brownian bridge process in the absence of an eclipse attack. This enables us to quantify the false alarm rate of the detector. Our detector can be implemented as a smart contract on the blockchain, offering a tamper-proof and reliable solution. Finally, we use numerical examples to compare the proposed eclipse attack detector with a detector based on the random forest model.
Introduction
Blockchain, an immutable ledger distributed across multiple users, relies on consensus among its users to share data. This paper studies adversarial attacks on blockchains, with a specific focus on eclipse attacks. In an eclipse attack, malicious users isolate a victim user, disrupting their ability to reach a consensus with the rest of the network. For example, if a user has eight incoming connections from other users, and an attacker controls all eight of those nodes, the attacker can refuse to relay any new blocks that rest of the network produce. Hence, detecting eclipse attacks are crucial for safeguarding blockchain networks.
Main results
To detect an eclipse attack, we propose a non-parametric change detection algorithm that identifies changes in the Fréchet mean and variance (these are topological generalizations of mathematical expectation and variance) within a sequence of randomly evolving blockchain communication networks (BCNs). We exploit the Johnson-Lindenstrauss (JL) lemma to extract essential features from the large-dimensional BCN, ensuring that the test statistic is approximately preserved. In blockchain, a smart contract is a computer program that automatically executes a task based on a pre-specified conditions. Our proposed detector can be implemented as a smart contract on blockchain to detect an eclipse attack using a network monitor; this information can then be relayed to the blockchain users.
Detecting eclipse attack on a blockchain network as a change detection problem
In this section, we formulate detecting eclipse attacks on a blockchain network as a change detection problem and present our detection algorithm.Model for eclipse attack
We begin by modeling the BCN as a directed graph and defining its adjacency matrix.
A BCN is represented as a directed graph \(G=(V,E)\in\mathcal{G}\), where \(\mathcal{G}\) is the graph space comprising \(p\) vertices. Each vertex has \(q\) outgoing edges.
The adjacency matrix \(A_{G}\in\mathbb{R}^{|V|\times|V|}\) of the BCN \(G\) is defined as follows:
\[ A_{G}(i,j)=\begin{cases} 1, & \text{\(\exists\) an edge from the vertex \(j\)}\\ &\text{to the vertex \(i\)} \\ 0, & \text{otherwise} \end{cases} \]Consensus in blockchain relies on peer-to-peer (P2P) communication. The BCN serves to illustrate the flow of information among blockchain users.
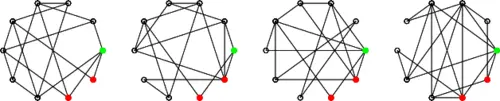
In the absence of an eclipse attack, the BCN at each time \(t\) resembles a random graph with uniform distribution. Here, each user simply selects \(q\) neighbors in a random and uniform manner to share information. However, during an eclipse attack, malicious users target victim users with substantial computational power. These malicious actors choose their neighbors in a non-uniform manner to disrupt the consensus of the victim users.
In this work, we assume: (1) When all users select their neighbour honestly using the blockchain communication protocol, the random BCN \(G\) follows an unknown but fixed distribution \(P_2\). (2) The eclipse attack strategy is time-invariant (For an eclipse attack, multiple malicious users must communicate continuously with the victim user(s). A complex eclipse attack strategy can slow the communication rate and make the attack ineffective. Therefore, the assumption of a time-invariant eclipse attack strategy is justified.). Consequently, in the presence of an eclipse attack, the BCN \(G\) follows an unknown but fixed distribution \(P_1\). For instance, a common eclipse attack strategy employed by malicious users is to choose the victim users as their neighbors with a significantly higher probability compared to other users. Now, let's provide a formal definition of our model for the eclipse attack.
A blockchain is free from an eclipse attack if the random BCN, as represented by the graph \(G\), is sampled from \(\mathcal{G}\) following the distribution \(P_2\). Conversely, a blockchain is under an eclipse attack if the random graph \(G\) is sampled from \(\mathcal{G}\) following the distribution \(P_1\).
Now, let's consider an example of the distribution \(P_1\). Here, \(r\) malicious blockchain users, denoted as \(v_{p-q-1},v_{p-q},\ldots,v_{p}\in V\), choose \(v_1\in V\) as their victim.
For \(j=v_{p-q-1},v_{p-q},\ldots,v_{p}\in V\)Eclipse attack detection problem
We now formulate the eclipse attack detection problem as a change detection problem. The proposed detector operates on an offline dataset of BCNs (Note that changes in the BCN occurs at a faster rate than the addition of new blocks to the blockchain. This allows us to observe a substantial sample of BCNs before a double spend attack resulting from an eclipse attack is achieved. Therefore, using offline datasets for eclipse attack detection is practical.); the BCN can be monitored using a network monitor. We formulate the eclipse attack detection problem as a hypothesis testing problem.
The eclipse attack detection problem on a blockchain network is the following hypothesis testing problem
\[ H_0: G_1, G_2, \ldots, G_N \sim P_2 \] \[ H_1: \exists\; \tau\in\{1,\ldots,N\} \\s.t.\: \left\{\begin{array}{l} G_1, G_2, \ldots, G_{\tau-1} \sim P_2 \\ G_{\tau}, G_{\tau+1}, \ldots, G_N \sim P_1\end{array}\right. \]Test statistic for detecting eclipse attack
In this section, we present a test statistic to solve the eclipse attack detection problem. The proposed test statistic estimates changes in the mean and variance of the sequence of BCNs. However, the communication network do not lie in the Euclidean space. So, we use the concept of Fréchet mean and variance, a topological generalization of mean and variance.
To calculate the Fréchet mean and variance, we define a distance metric \(d\) on the space of the BCN \(\mathcal{G}\). This metric measures the dissimilarity between two BCNs \(G_1\) and \(G_2\) using the Frobenius norm.
The distance \(d\) between two BCNs \(G_1,G_2\in \mathcal{G}\) is defined as the Frobenius norm of the difference between their adjacency matrices.
\[ d(G_1,G_2)=\left(\sum_{i,j}|A_{G_1}(i,j)-A_{G_2}(i,j)|^2\right)^{\frac{1}{2}} \]The test statistic partitions the sequence of BCNs into two parts. The goal is to determine if the BCNs in these two components are sampled from the same or distinct distributions. To achieve this, the test statistic examines the Fréchet mean and variance of the BCNs in each component.
Under the null hypothesis \(H_0\), i.e., absence of an eclipse attack on the blockchain network, the Fréchet mean and variance of the BCNs in both parts are the same. Conversely, under the alternate hypothesis \(H_1\), the Fréchet mean and variance of the BCNs in these parts differ, signaling the presence of an eclipse attack.
Before introducing our test statistic for eclipse attack detection, we define several mathematical quantities that rely on the adjacency matrices \(A_G\) of the sequence of BCNs. We also introduce the term \(n\), which represents an estimate for the change point \(\tau\) in the eclipse attack detection problem. For each \(n\in\{1,\ldots, N-1\}\), we proceed to define these quantities and present our test statistic.
The test statistic compares the Fréchet mean and variance of the BCNs \(G_1,G_2,\ldots,G_n\) and \(G_{n+1},G_{n+2},\ldots G_{N}\).
Let \(n\) denote the estimate for the change point \(\tau\) in the eclipse attack detection problem. The test statistic \(S_{n,N}\) is defined as follows:
\[ S_{n,N}=\frac{n(N-n)}{N^2\hat{\sigma}^2}\left\{\left(\hat{V}_{n}-\hat{V}_{N-n}\right)^2+\left(\hat{V}_{n}^C-\hat{V}_{n}+\hat{V}_{N-n}^C-\hat{V}_{N-n}\right)^2\right\} \]The test statistic \(S_{n,N}\) comprises two terms: the first term estimates the change in Fréchet variance, while the second term estimates the change in the Fréchet mean of the BCNs in the two components.
Dimensionality reduction of the adjacency matrices
In this section, we use the JL lemma () to reduce the dimension of the adjacency matrix. Remember that the proposed test statistic is computed using the sequence of adjacency matrices for the BCNs. The number of elements in the adjacency matrix grows as the square of the number of blockchain users. Hence, it is necessary to reduce the dimension of the adjacency matrices \(A_G\) to decrease the computational cost of the test statistic (S_{n,N}\).
In this work, we leverage the JL lemma to project the adjacency matrices of BCNs into a lower-dimensional subspace while approximately preserving the test statistic.
Given any \(\epsilon \in (0, 1)\) and an integer \(N\), let \(k\) be a positive integer satisfying
\[ k \geq \frac{24}{3 \epsilon^2 - 2 \epsilon^3} \log N \]For any set \(A\) containing \(N\) points in \(\mathbb{R}^m\), there exists a mapping \(f: \mathbb{R}^m \rightarrow \mathbb{R}^k\) such that for all (x, y \in A\), the following inequality holds:
\[ (1-\epsilon)\|x-y\|^2 \leq \|f(x)-f(y)\|^2 \leq (1+\epsilon)\|x-y\|^2 \]Now, we apply the JL lemma on the adjacency matrices to obtain the projected adjacency matrices.
The projected adjacency matrices, denoted as \(\hat{A}_G\) for the BCNs are obtained by applying the JL lemma to the adjacency matrices with an appropriately chosen value of \(\epsilon\). Equivalently,
\[ \hat{A}_{G_i}=f(A_{G_i}),i=1,2,\ldots,N \]Comparison between the adjacency matrixof the BCN and the projected adjacency matrix
To apply the JL lemma, we first vectorize the adjacency matrix \(A_G\). Denote the vectorized \(A_G\) as \(X\). Then, we compute a suitable linear transformation \(Q\) that satisfies the JL lemma for the chosen value of \(\epsilon\). Now,Algorithm for detecting eclipse attack
Having developed the necessary mathematical tools, we present the eclipse attack detection algorithm. Given the large dimension of the BCN, we initially employ the JL lemma to reduce dimensionality while approximately preserving the test statistic. We also assume that the eclipse attacks do not occur near the endpoints.
Algorithm: Detecting Eclipse Attack on a Blockchain Network
Input: Sequence of adjacency matrices of the random BCNs
Step 1. Dimensionality Reduction: Compute the projected adjacency matrices \(\hat{A}_G\) using the JL lemma.
Step 2. Test Statistic: Compute the test statistic \(S_{n,N}\) using \(\hat{A}_G\) for \(n = 1, 2, \ldots, N - 1\) such that \(\frac{n}{N} \in (\delta, 1 - \delta)\)
Step 3. Asymptotic Quantile: Choose a significance level \(\alpha \in [0, 1]\). Compute the \((1 - \alpha)\)-quantile \(q_{1 - \alpha}\) of the distribution:
where \(\mathbb{B}(t)\) is a Brownian bridge on \([0,1]\) with covariance:
Step 4. Decision Rule: If
Then: Return "No eclipse attack detected."
Else: Return "Eclipse attack detected at time"
Let \( k \) denote the dimension of the adjacency matrices. Then, the computational complexity of the algorithm is:
where \( \mathcal{G} \) is defined in the original adjacency matrix expression.
To summarize, we designed an algorithm to detect an eclipse attack on a blockchain network. The test statistic is based on Fréchet change detection, and the JL lemma is used for dimensionality reduction.
Weak convergence of test statistic
Our first result (Theorem 1) analyzes the asymptotics of the test statistic \(S_{n,N}\) under the null hypothesis \(H_0\), i.e., absence of an eclipse attack on the blockchain network. Note that \(\{S_{n,N},n=1,2,\ldots,N-1\}\), represents a discrete-time stochastic process. As is customary in weak convergence analysis, we first construct a continuous time stochastic process \(S_N(N t)\) by interpolating the discrete time test statistic process \(\{S_{n,N}\}\).shows that as \(N\rightarrow \infty\), the scaled test statistic continuous time stochastic process \(T_N(t)\) converges weakly (in Skorohod metric) to the square of a Brownian bridge stochastic process. Note that the weak convergence approach deals with the convergence of scaled sequences of the test statistic that are treated as stochastic processes rather than random variables. Thus, the weak convergence approach specifies convergence for the entire trajectory of the test statistic of the detection algorithm.
Assume that the eclipse attack do not occur near the endpoints, i.e., \(\frac{\tau}{N}\in[\delta,(1-\delta)]\) for some \(\delta>0\), where \(\tau\) is defined in. Then, under \(H_0\) (absence of an eclipse attack), the scaled test statistic process converges weakly:
\[ T_N(t)\Rightarrow \mathcal{B}^2(t) \]Also, the continuous mapping theorem implies
\[\max_{t\in[\delta,(1-\delta)]}T_N(t)\Rightarrow \max_{t\in[\delta,(1-\delta)]}\mathcal{B}^2(t) \]Here \(\Rightarrow\) denotes weak convergence (Weak convergence in functional space is a generalization of the weak convergence in distribution for random variables. A sequence of probability measures \(\mu_n\) converges weakly to the probability measure \(\mu\) if, for all bounded and continuous test functionals \(f\), the expected value of \(f\) with respect to \(\mu_n\) converges to the expected value of \(f\) with respect to \(\mu\), i.e., \(\mathbb{E}_{\mu_n}[f] \rightarrow \mathbb{E}_{\mu}[f]\)). \(\mathcal{B}\) is a standardized Brownian bridge process (A standardized Brownian bridge on \([0,T]\) is a continuous-time stochastic process whose probability distribution is the conditional probability of the Weiner process \(W(t)\) subject to the condition that \(W(0)=W(T)=0\) with the covariance function \(C(t_1, t_2)=1,\,0\leq t_1 \leq t_2\leq 1\).) with the covariance function \(C(t_1, t_2)=1,\,0\leq t_1 \leq t_2\leq 1\).
ProofRefer the arXiv paper Eclipse Attack Detection on a Blockchain Network as a Non-Parametric Change Detection Problem .
Convergence to a Brownian bridge instead of Brownian process in Theorem 1 is intuitive because \(T_N(t)\propto t(1-t)\). Theorem 1 is used in the algorithm to detect an eclipse attack. In practice, we declare the presence of an eclipse attack on a blockchain network if the maximum of the scaled test statistic exceeds the \(0.95\) quantile, denoted as \(q_{0.95}\), of the distribution \(\max_{t \in [\delta,1-\delta]}\mathcal{B}^2(t)\).
Our second result () investigates the test statistic \(S_N(N t)\) under \(H_1\), i.e., presence of an eclipse attack on the blockchain network. This result estimates the onset of the eclipse attack. Before presenting the theorem, we need to define the limiting test statistic \(S(N t)\):
Here, the test statistic \(S_N(N t)\) converges to \(S(t)\) in probability.
Assume that the eclipse attack do not occur near the endpoints, i.e., \(\frac{\tau}{N}\in[\delta,(1-\delta)]\) for some \(\delta>0\). Then, under \(H_1\) (presence of an eclipse attack), the maximum of the limiting test statistic \(S(N t)\) occurs at the onset, \(\tau\) of the eclipse attack:
\[ \lim_{N\rightarrow\infty}\frac{\tau}{N}=\arg\max_{t \in [\delta,(1-\delta)]}S(t) \]Let \(\tau_N=N\arg\max_{t \in [\delta,(1-\delta)]}S_N(N t)\). Then for \(\gamma>0\) the following holds
\[ \mathbb{P}{\left|\frac{{\tau}_{N}-\tau}{N}\right|>\gamma}\rightarrow 0 \]Refer the arXiv paper Eclipse Attack Detection on a Blockchain Network as a Non-Parametric Change Detection Problem .
The second statement of Theorem 2 gives an error bound for estimating the onset of the eclipse attack using finite samples of BCNs. Theorem 2 is used in the algorithm to estimate the onset of the eclipse attack using the discrete-time test statistic \(S_{n,N}\).
Effect of the processed adjacency matrices on the test statistic
Our final result () compares the test statistic computed using the projected adjacency matrices and the original adjacency matrices of the BCN. It shows that the false positive alarm rate of the detector is higher when the test statistic is computed using the projected adjacency matrix \(\hat{A}_G\).
Let \(S_N(N t)\) denote the test statistic computed using the original adjacency matrices. Let \(\tilde{S}_N(N t)\) denote the test statistic computed using the projected adjacency matrices. Under \(H_0\), as \(N\rightarrow\infty\), using projected adjacency matrices to compute the test statistic leads to a higher false positive alarm rate:
\[ \lim_{N\rightarrow\infty}\tilde{S}_{N}(N t) \geq \lim_{N\rightarrow\infty}S_{N}(N t) \]Here, the convergence to the limit is in probability. Furthermore,
\[ \lim_{N\rightarrow\infty} \tilde{S}_N(N t) \geq \frac{5\epsilon\, t(1-t)V}{\hat{\sigma}^2} \]where \(V=\lim_{N\rightarrow\infty}\hat{V}\); \(\epsilon\in(0,1)\); and \(\hat{\sigma}^2\) is the empirical variance.
Refer the arXiv paper Eclipse Attack Detection on a Blockchain Network as a Non-Parametric Change Detection Problem .
In summary, we have presented three key results on the test statistic for detecting an eclipse attack: 1) Under the null hypothesis \(H_0\), the first result ensures weak convergence of the maximum of the scaled test statistic to the maximum of the square of the Brownian bridge process. 2) Under the alternate hypothesis \(H_1\), the second result estimates the onset of the eclipse attack on the blockchain network. 3) The third result investigates the impact on the false alarm rate of the detector when using the projected adjacency matrices to compute the test statistic.
Numerical results






Conclusion
This paper addressed the problem of detecting an eclipse attack on a blockchain network by designing a non-parametric change detection algorithm. In an eclipse attack, malicious users isolate a victim user, disrupting their ability to reach a consensus with the rest of the network.
Our eclipse attack detection approach involved estimating changes in the Fréchet mean and variance of the BCN. We showed that the test statistic for the proposed eclipse attack detector weakly converges to a Brownian bridge process. This allowed us to quantify the false alarm rate of the detector. The proposed statistical detector can be implemented as a smart contract on top of the blockchain to mitigate the impact of an eclipse attack. Finally, we used ROC curves to characterize the performance of the proposed eclipse attack detector and the RFM based detector.
In future work, we will explore: (1) detecting an eclipse attack on a blockchain network with time-varying blockchain users, (2) theoretical bounds on the accuracy of the test statistic when the BCNs are observed in noise, (3) refining the proposed test statistic to effectively detect an eclipse attack near endpoints, and (4) generalizing the change detection algorithm to address time-varying eclipse attack strategies. These extensions will improve the applicability and effectiveness of the proposed eclipse attack detection algorithm.
Acknowledgement
I would like to thank Dr. Brian Sadler for providing valuable feedback during the summer internship.
Reference
Eclipse Attack Detection on a Blockchain Network as a Non-Parametric Change Detection Problem
Author
Anurag Gupta is an M.S. graduate in Electrical and Computer Engineering from Cornell University. He also holds an M.Tech degree in Systems and Control Engineering and a B.Tech degree in Electrical Engineering from the Indian Institute of Technology, Bombay.
Comment
This policy contains information about your privacy. By posting, you are declaring that you understand this policy:
- Your name, rating, website address, town, country, state and comment will be publicly displayed if entered.
- Aside from the data entered into these form fields, other stored data about your comment will include:
- Your IP address (not displayed)
- The time/date of your submission (displayed)
- Your email address will not be shared. It is collected for only two reasons:
- Administrative purposes, should a need to contact you arise.
- To inform you of new comments, should you subscribe to receive notifications.
- A cookie may be set on your computer. This is used to remember your inputs. It will expire by itself.
This policy is subject to change at any time and without notice.
These terms and conditions contain rules about posting comments. By submitting a comment, you are declaring that you agree with these rules:
- Although the administrator will attempt to moderate comments, it is impossible for every comment to have been moderated at any given time.
- You acknowledge that all comments express the views and opinions of the original author and not those of the administrator.
- You agree not to post any material which is knowingly false, obscene, hateful, threatening, harassing or invasive of a person's privacy.
- The administrator has the right to edit, move or remove any comment for any reason and without notice.
Failure to comply with these rules may result in being banned from submitting further comments.
These terms and conditions are subject to change at any time and without notice.
Similar content




Past Comments